Secure Web Apps with Trust IAP in Georgia
Securing Web Applications in Georgia with Trust IAP
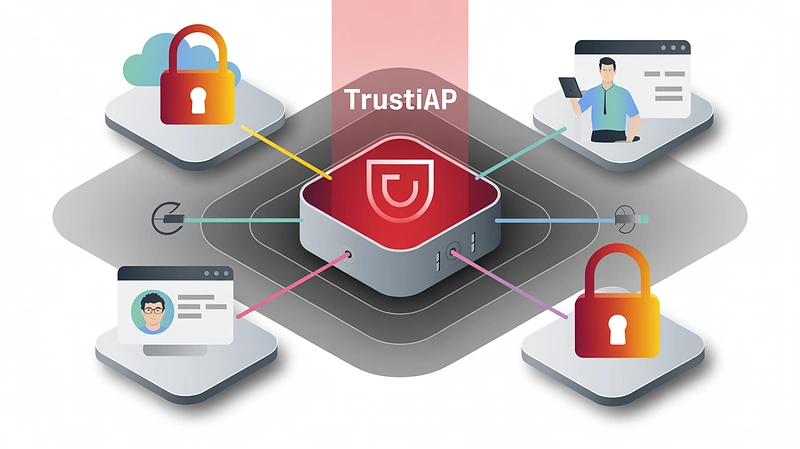
Trust IAP (Identity-Aware Proxy) offers a sophisticated solution for controlling user access to web applications. Functioning as an intelligent proxy gateway, it verifies access based on user identity, roles, and other authentication criteria. The primary objective is to provide secure access to your web systems without the complexities of traditional VPNs, enhancing user experience while bolstering security. Given that approximately 65% of cyberattacks target web applications and software, the need for such a solution is critically important for businesses operating in Georgia.
Key Benefits of Trust IAP
Enhanced Security
- Role-based access: Ensures that only authorized users gain access based on their defined roles, groups, and context.
- Protection against web vulnerabilities: Mitigates attacks targeting web application vulnerabilities, including spoofing and brute-force attempts.
Robust Authentication
- Multi-Factor Authentication (MFA): Employs modern authentication methods such as push notifications, TOTP/HOTP codes, and passwordless QR codes.
- Password protection: Even if a user’s password is compromised, access remains secure due to the requirement of a second authentication factor.
Simplified Access Management
- Single Sign-On (SSO): Supports industry standards like SAML, CAS, OpenID Connect, NTLM, and Basic Auth, streamlining authorization across multiple systems with a single login.
Comprehensive Auditing and Reporting
- Audit trails and logging: Records all user requests, maintains logs, and seamlessly integrates with SIEM systems for enhanced security monitoring.
High Availability and Scalability
- Reliability: Offers support for 5×8 and 7×24 operation modes with a guaranteed uptime of 99.999%.
- Scalability: Designed to efficiently handle systems with millions of users.
Modern Security Approach
- Zero Trust Architecture: Based on Zero Trust principles and a defense-in-depth strategy.
- User-Friendly Design: Ensures a seamless user experience without the need for additional software installations or complex procedures.
Trust IAP provides a solution for ensuring secure, controlled, and user-friendly access to web systems, minimizing risks and complexity.
Ideal Use Cases for Trust IAP in the Georgian Market
Trust IAP is well-suited for organizations in Georgia that rely on web applications, interfaces, control panels, internal services, web APIs, and administrative web interfaces. Key use cases include:
- Internal Portals and Web Systems: Secure access for employees and partners to internal web applications over the internet, ensuring that only authorized users with appropriate roles gain entry.
- Administrative Panels: Safeguards control panels, DevOps tools, and console web interfaces, preventing unauthorized access without authentication and verification. These are often high-value targets for cybercriminals.
- Partner and Client Access to Web Services: Facilitates secure access for external users or partners to specific system modules with role-based permissions, eliminating the need for VPNs or uncontrolled access.
- Microservices and API Integrations: Protects individual web services and APIs by verifying that requests originate from authorized users.
- Compliance-Driven Organizations: Supports adherence to security standards and audit requirements through robust logging and access control capabilities.
Practical Applications of Trust IAP
- Manufacturing Company: Integrates Trust IAP with an internal production management tool, providing secure access to authorized users based on their roles and requiring Multi-Factor Authentication.
- Software Startup: Protects its client-facing web service’s back-office by deploying Trust IAP to ensure only legitimate administrators with the correct permissions can access the system.
- IT Integrator: Uses Trust IAP as a unified front-end for managing hundreds of client systems, streamlining access based on user rights without the need for individual VPN configurations.
Technical Capabilities
- Access Control: Granular control over user access based on roles, groups, and policies.
- Strong Authentication (MFA): Support for push notifications, TOTP/HOTP codes, QR codes, and passwordless authentication.
- Single Sign-On (SSO): Compatibility with SAML, CAS, OpenID Connect, NTLM, and Basic Auth standards.
- Web Attack Protection: Prevention of brute-force attacks, protection against spoofing, and blocking exploitation of vulnerabilities.
- Auditing and Logging: Comprehensive logging of all requests, integration with SIEM systems, and reporting for audit purposes.
- Performance and Scalability: Lightweight and fast solution with support for thousands to millions of users and minimal latency.
- Reliability and Availability: Operation in 5×8 and 7×24 modes with a guaranteed uptime of 99.999%.
- Modern Security Concepts: Implementation of Zero Trust and Defense-in-Depth security strategies.
- Ease of Use: No need for additional software installations with an intuitive interface.
Trust IAP offers a comprehensive web security solution at the access layer.
